What if the greatest threat at sea is no longer what attacks… but what disappears?
🧠 Waides Feed
Across the Gulf of Guinea, a quiet transformation is unfolding — one that is far less visible than piracy, yet potentially more dangerous.
For years, maritime insecurity in this region was defined by direct attacks: hijackings, kidnappings, and armed confrontations. But today, that model is evolving. The threat is no longer always seen.
Ships are beginning to disappear — not physically, but digitally.
Through the deliberate disabling of AIS (Automatic Identification System), vessels effectively remove themselves from global tracking networks. These “ghost ships” operate in a space where visibility ends and control weakens.
As we will explore in our deeper breakdown of maritime intelligence systems, the modern ocean is no longer just a physical domain. It is a data-driven environment, where presence is defined by signal, not sight.
And when that signal disappears, the system loses its ability to respond.
The future of security is no longer about force.
It is about visibility.
💡 Why It Matters / Public Context
The threat has shifted from visible attacks to invisible operations.
When ships disappear from tracking systems, control over maritime space begins to collapse.
For Nigeria, this means hidden economic losses and reduced authority over its own waters. For the world, it raises concerns about the integrity of global shipping systems.
📘 What are “Ghost Ships” and AIS-Disabling?
“Ghost ships” are vessels that deliberately switch off their AIS — a tracking system designed to monitor ship identity, location, and movement.
AIS is essential for:
- Navigation safety
- Maritime monitoring
- Security enforcement
When disabled:
👉 The ship becomes invisible to tracking systems
In simple terms:
A ghost ship is not unseen — it is unregistered within the system that controls the sea
🌐 Real Examples / Current Use
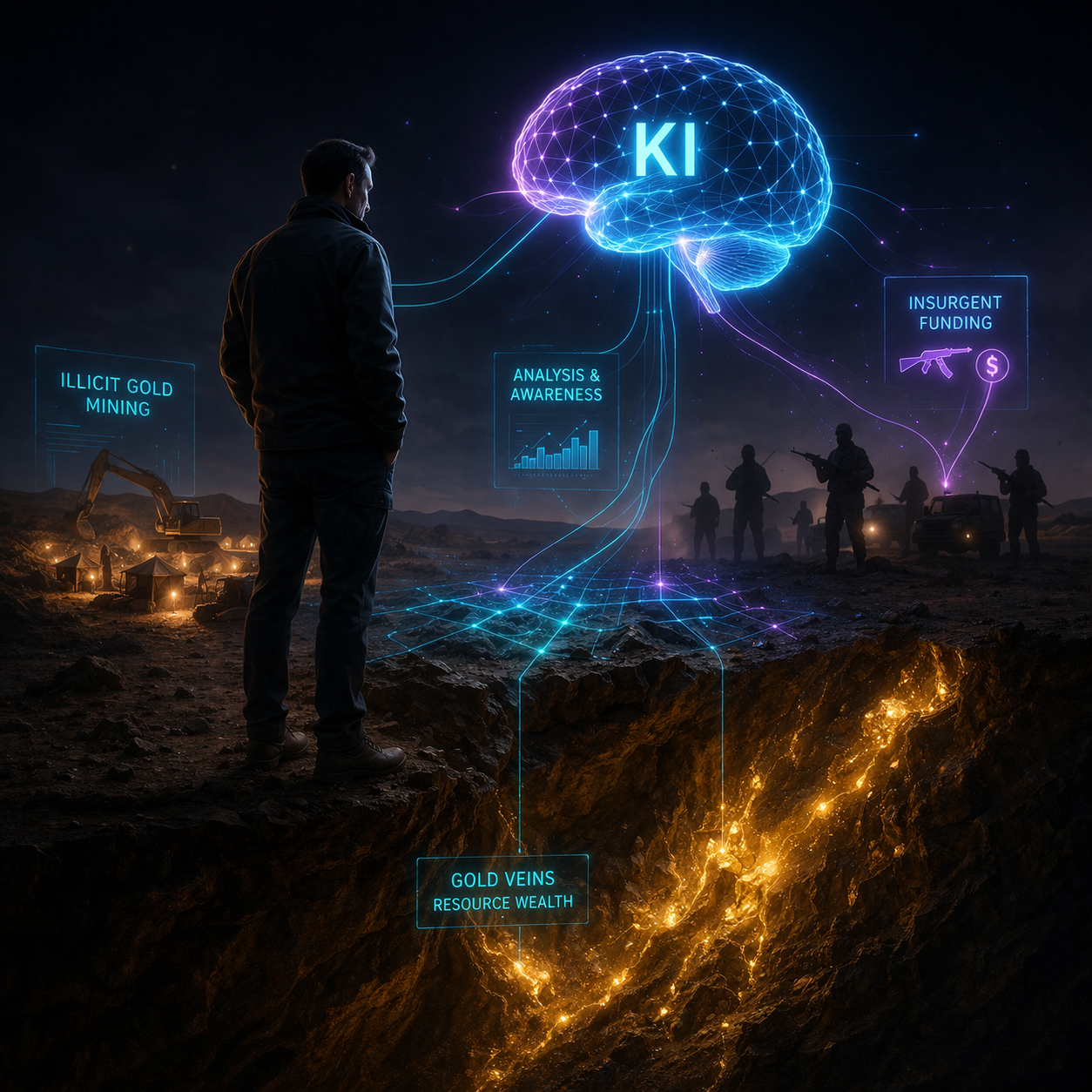
- Ships disabling AIS to conduct illegal oil transfers at sea
- Unregistered cargo movement across West African waters
- Reduced visibility in maritime monitoring systems
- Increasing sophistication of covert shipping networks
This reflects a broader shift we are seeing in global systems — where enforcement pressure leads to more advanced evasion strategies.
As we will explore in our analysis of global trade security evolution, systems adapt… but so do the threats within them.
⚙️ How It Works / Why It Matters
Modern maritime security relies on data visibility.
The system works like this:
- Ships transmit location via AIS
- Authorities monitor movement
- Anomalies trigger response
But when AIS is disabled:
👉 The system breaks at its foundation
No signal = no detection
No detection = no control
Why this matters:
👉 The ocean becomes a space where activity exists without accountability
🕰️ Historical Context
Maritime threats have evolved over time:
- Past: Direct confrontation (piracy)
- Present: Covert operations (AIS disabling)
Historically, every improvement in security creates a shift in threat behavior.
👉 When visibility increases, threats move into invisibility
This is not a new pattern — but its scale in modern maritime systems is unprecedented.
🧬 KI Insight
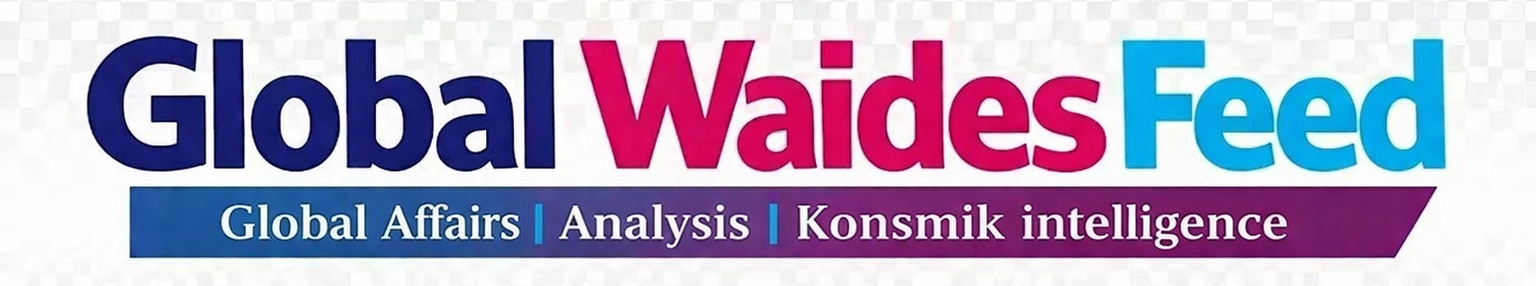
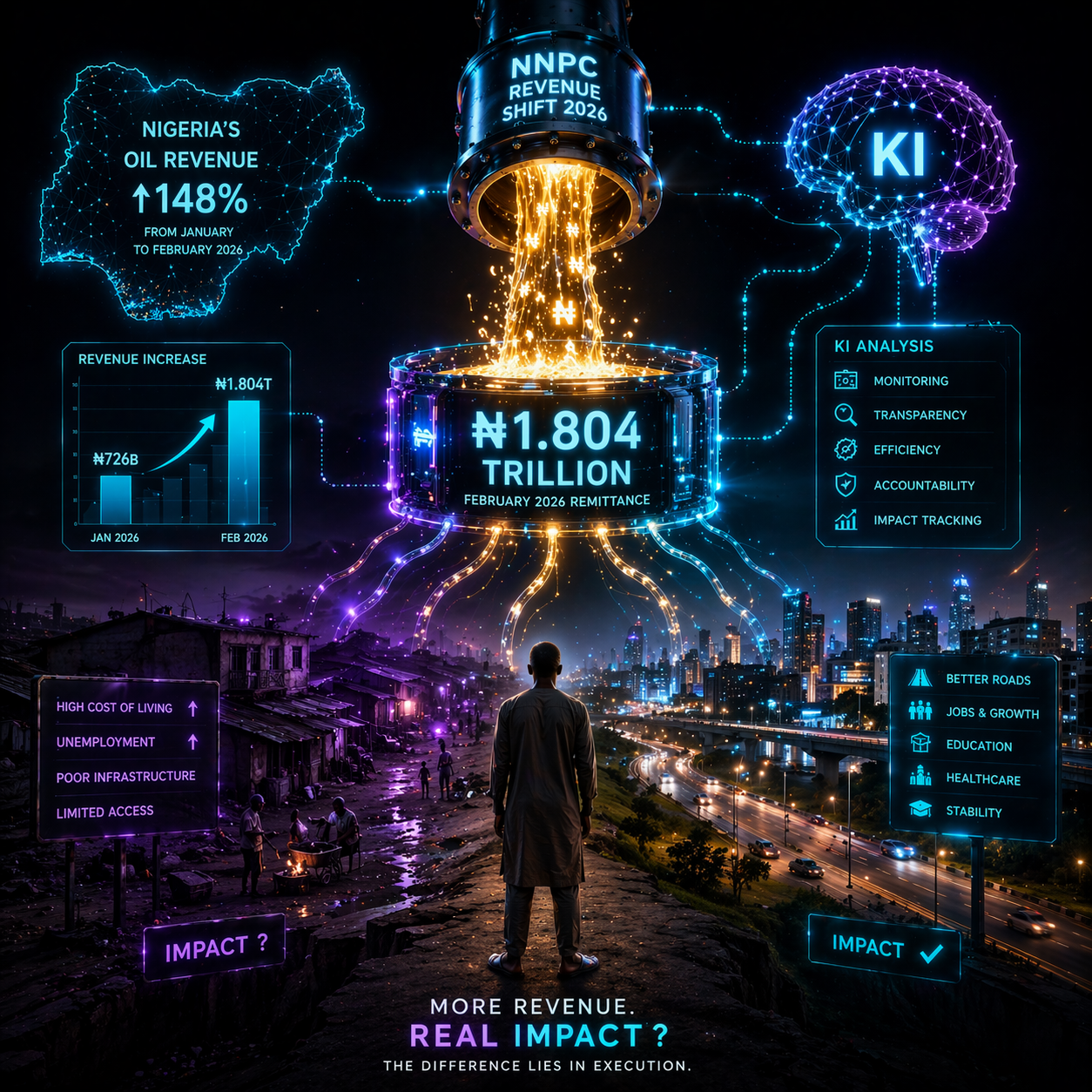
According to KI analysis, the rise of ghost ships represents a structural shift in maritime risk — from physical dominance to informational control.
The system is no longer defined by who controls the sea physically, but by who controls visibility within the system.
Core dynamic:
👉 Visibility = control
👉 Invisibility = vulnerability
From the perspective of Konsmik Civilization, this highlights a deeper truth:
👉 Systems that depend on data must also secure the integrity of that data
Opportunities:
- Deployment of advanced satellite and AI-based tracking systems
- Strengthening maritime intelligence networks
- Integration of real-time data monitoring across regions
Risks:
- Expansion of illegal oil trade
- Significant revenue loss for Nigeria
- Undetected environmental and economic damage
- Loss of global trust in regional shipping routes
In Konsmik Civilization, maritime systems would be designed with layered visibility — combining physical, digital, and predictive monitoring to eliminate blind spots before they emerge.
🌍 For Konsmik Civilization
In Konsmik Civilization:
- Visibility is continuous and multi-layered
- Systems do not rely on a single point of data
- Detection is predictive, not reactive
System flow:
- Monitor signals and patterns
- Detect anomalies instantly
- Respond before disruption occurs
Outcome:
A maritime system where disappearance is not possible.
🛠️ Solution Layer
Micro (Individual Awareness):
- Understand how global systems affect national stability
Meso (Regional):
- Strengthen cooperation among Gulf of Guinea states
- Share maritime intelligence and tracking systems
Macro (Government):
- Invest in satellite-based tracking technologies
- Enforce strict AIS compliance policies
- Develop integrated maritime surveillance systems
🌌 Konsmik Reality
The ocean has not changed.
But the system that governs it has.
And in that system,
what cannot be seen…
cannot be controlled.
The rise of ghost ships is not just a maritime issue.
It is a reflection of a deeper shift:
👉 Power is moving from physical presence to informational control
🔮 Forecast
Short-Term (1–2 years):
- Increase in AIS-disabling incidents
- Growth of invisible maritime operations
Medium-Term (3–5 years):
- Adoption of advanced monitoring technologies
- Stronger enforcement of maritime tracking systems
Long-Term (5–10 years):
- Maritime systems become fully data-integrated
- Regions that fail to secure visibility face ongoing vulnerability
❓ FAQ
What is AIS in shipping?
AIS is a tracking system that shows a ship’s identity and location.
Why do ships disable AIS?
To avoid detection, often for illegal or unregulated activities.
What are ghost ships?
Ships that operate without active tracking, making them invisible to monitoring systems.
Does this affect Nigeria?
Yes, it impacts revenue, security, and control over maritime space.
🧠 Closing Impact
The threat is no longer what approaches openly.
It is what operates without being seen.
🌍 Reflection Question
If control depends on visibility,
what happens when entire systems learn how to disappear?











Leave a Reply